Age and ID verification that stores nothing.
OFCOM-ready. GDPR by design. Verify age & ID from sources your users already have : their bank, their Govt portal login. No selfies. No documents. No PII on any server.
The problem with identity verification today
Every verification creates a copy of sensitive data. Every copy is a breach waiting to happen.
| Traditional (Doc + Selfie) | Reclaim Protocol | |
|---|---|---|
| User uploads government ID | ✅ Yes | ❌ No |
| Selfie / biometric collected | ✅ Yes | ❌ No |
| PII stored on server | ✅ Yes. Retained up to 3 years | ❌ Never touches a server |
| Breach risk | 🔴 High. Data held on server | 🟢 Zero. There's nothing to leak |
| Spoofable by minors | 🔴 Yes. Screen scanning, AI-generated docs | 🟢 No. Proof comes from authenticated session |
| Requires app download | Sometimes | ❌ No. Works fully on browser |
| GDPR data minimization | ⚠️ Difficult. You typically hold more data than you need | ✅ By design. Only the absolutely required data is extracted |
How it works: 30 seconds. 3 steps.
User logs in
The user logs into a trusted source they already have an account with: a bank, mobile carrier, health portal, or government service. Reclaim never sees their credentials.
The data is extracted
Only the specific data point you need is selected — e.g., "age = 42". Nothing else is extracted. Nothing else is shared.
A cryptographic proof is generated
A zero-knowledge proof is created on the client's device, verifying the data came from the claimed source and hasn't been altered. The proof is cryptographically tied to the source's TLS certificate. Tamper-proof. Unforgeable.
How we compare
| Yoti | Persona | Reclaim Protocol | |
|---|---|---|---|
| Method | Selfie age estimation | Document upload + selfie | Login into govt portal, bank etc |
| PII collected | Facial biometrics | Govt ID + face | None |
| Data stored | Yes — processed on server | Yes — claims 3-day deletion | Nothing. Ever. |
| Deepfake-proof | NoSelfie estimation can be spoofed with AI-generated faces | NoDocuments and selfies can be forged with AI | YesProof is from an authenticated TLS session. Nothing to forge. |
| Known incidents | €950K fineSpain's AEPD fined Yoti for biometric data handling, invalid consent, and excessive data retention | 70K IDs exposed~70,000 government-issued ID images exposed via customer service vendor. Discord publicly cut ties with Persona. | NoneNo personal data is collected, processed, or stored. Nothing exists to breach. |
| If breached, what leaks? | User face scans | Government IDs, selfies | Nothing. No data exists. |
| Your liability if vendor is breached | You're liableYou're the data controller. Biometric data is GDPR special category. | You're liableYou're the data controller. ID documents are personal data. | No liabilityNo personal data was processed. No breach notification required. |
| GDPR burden | HighBiometric data = special category. Requires explicit consent + DPIA. | HighID document retention requires lawful basis + data minimization proof. | MinimalNo personal data processed. Data minimization by design. |
| Integration time | Days to weeks | Days to weeks | Hours |
Read our blog on how to comply with OFCOM and GDPR in tandem
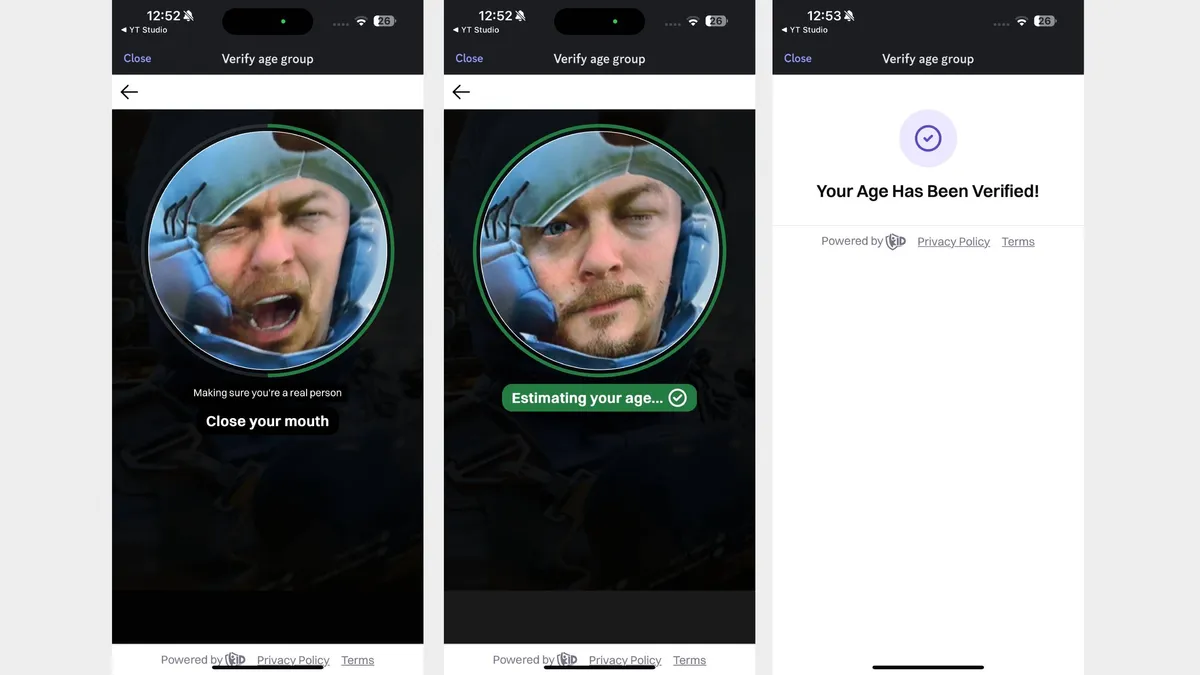
Try it out yourself
Countries being added to coverage at a rapid pace. Learn More
Regulatory FAQ
| Country | Regulation | Status | Note |
|---|---|---|---|
| 🇬🇧 United Kingdom | Online Safety Act (OFCOM) | ✅ | Aligns with "reusable digital identity" |
| 🇪🇺 European Union | Digital Services Act (Art. 28) | ✅ | Matches EU zero-disclosure blueprint |
| 🇫🇷 France | Loi SREN (Arcom) | ✅ | Fits double-anonymity principle |
| 🇩🇪 Germany | Youth Protection Act (KJM) | ⚠️ | Requires formal KJM assessment |
| 🇮🇳 India | DPDP Act & Rules 2025 | ✅ | DigiLocker/Aadhaar explicitly approved |
| 🇦🇺 Australia | Online Safety Act (eSafety) | ☑️ | Awaiting eSafety technical standards |
| 🇧🇷 Brazil | Digital ECA (Lei 15.211) | ☑️ | Govt ID explicitly permitted |
| 🇺🇸 United States | COPPA (FTC) | ☑️ | FTC incentivizes age verification |
| 🇨🇦 Canada | Bill S-210 / Bill C-63 | ✅ | Privacy-preserving explicitly required |
Verify identity without fraud and data breaches
Verify identity, age, and citizenship directly from government portals. No documents to review, no fraud to worry about.