Global. Compliant. 45%+ conversion rates. Fully private & secure.
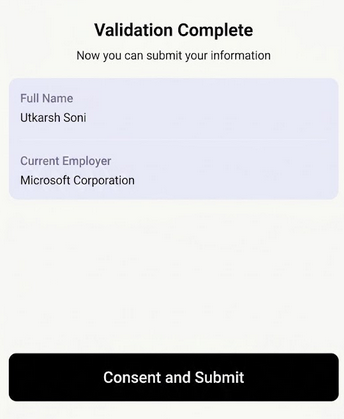
Verify employer and gross income from today's payroll. Most solutions rely on stale databases or phishing websites. Huge liability.
Read morePull live enrollment directly from universities. Not guessing using a .edu email, not using a transcript upload that's trivial to fake these days.
Read moreInstant tier verification across 100+ airlines and hotels. No screenshots, no email back-and-forth. This industry is ridden with AI generated fraud.
Read moreThe protocol uses zero-knowledge cryptography to fetch a single, verified fact straight from the issuing source — never seeing the user's credentials, never storing their data.
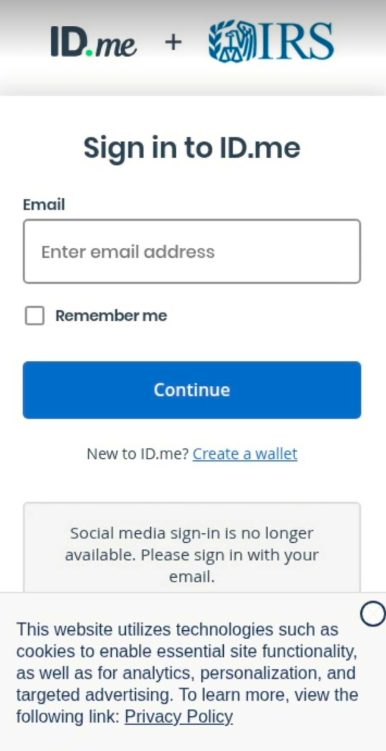
Your user signs into their university, employer, airline, or bank as they always do. Not an unfamiliar phishing site. Familiarity builds trust.
Name, enrollment status, tier, age. Only the field you asked for. Everything else stays on-device. No PII leaks. Consistent with GDPR data minimization laws.
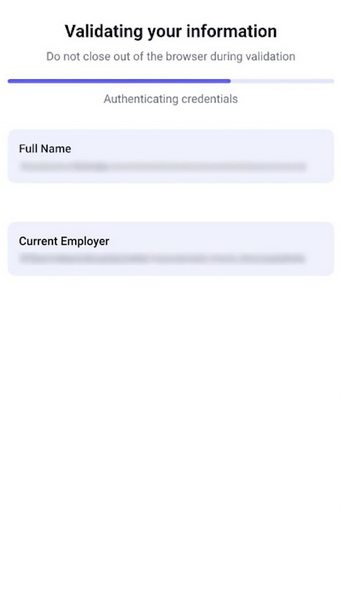
A zero-knowledge proof is generated on device. Akin to a digital notary. Unforgeable. You receive the proof on user consent. You can verify yourself.
Tricking users into handing over a username and password to your verification vendor isn't a UX shortcut — it's a credential-phishing pattern. The regulator agrees. Your users do too.
With Reclaim, the user logs in on the real source (the employer, the university, the airline). We never see the password. All the verification happens on the browser, not our backend.
Across customers in airline loyalty, mortgage & lending, and background checks — happy to introduce on request.

“We started this research in 2022 because we could see what AI was about to do to the internet. Documents would become trivially forgeable; the verification stack the entire economy runs on would silently break. We built Reclaim Protocol so every fact you verify is straight from the source — no document uploads, no phishing. All verified using cryptography, so even a single byte or pixel tampered with is caught trivially.”
“The better the AI models get, the more fraud there is — and the more you'll need Reclaim Protocol.”
AI fakes any document in 10 seconds. Regulators are watching more closely than ever before. Your users are globally distributed.
The old guard wasn't built for any of it:
Grab an API key, paste the SDK snippet, ship to staging this afternoon. Built by engineers, for engineers.
// 1. Initialize the verifier import { ReclaimProofRequest } from '@reclaimprotocol/js-sdk'; const req = await ReclaimProofRequest.init( APP_ID, APP_SECRET, 'university-enrollment' // or 'employer-income', 'airline-tier'… ); // 2. Send the user through the flow await req.triggerReclaimFlow(); // 3. Receive a cryptographic proof. Done. req.onProof(proof => { user.grantStudentDiscount(proof); });
Plug in a test API key in 10 lines of code. Throw your fraud team's hardest examples at it. If we can't catch it, you don't pay.